KNOWLEDGE GURU DATA SECURITY INFORMATION
Architecture
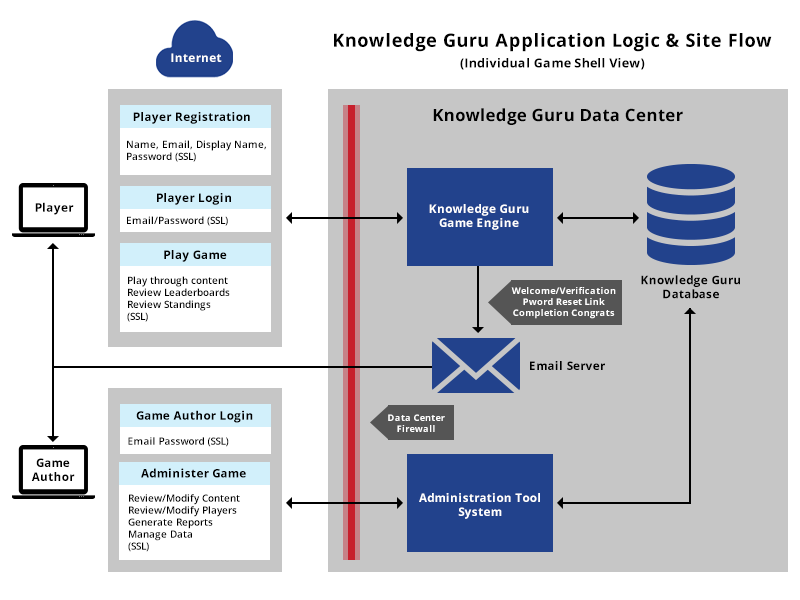
The diagram below shows how Knowledge Guru’s architecture manages information flow, authentications, encryption on data transfer and different data touch points.
Data
1. What type of data is transferred to the Knowledge Guru? (Example of data fields)
Players provide their name and email, and then create a password and display name for use with in-game leaderboards.
Game Authors provide their name and email, and then create a password and enter learning game content into the system via a security Game Creation tool. Learning game content includes topic names, learning objectives, and questions/response options.
System Administrators provide their name and email and then create a password. They can input game author names and emails as well as create game names for Knowledge Guru games (e.g. Guru)
Data Transfer
1. How is the data transferred?
HTTPS/SSL
2. What is the frequency of the data transfer?
Very infrequent, after initial account setup only the email and password are provided for authentication.
3. How is authentication done for accessing the data to be transferred?
Once players or Game Authors have created an account, they provide their email and password to authenticate all future access. This authentication is handled via a secure HTTPS/SSL connection and the password is encrypted prior to storage. We cannot view the actual password values in our system, we can only encrypt provided values at login and match them for authentication purposes.
Data at Rest
1. How is the data stored in the Knowledge Guru platform?
Data is stored in an Amazon Web Services RDS running MySQL.
2. What is the physical location of the data that will be stored?
We do not store data on our own premises. Amazon hosts our solution. Its primary data center is located in the US-EAST region (N. Virginia).
3. What are the access controls around this stored data?
Physically speaking, the datacenter uses state-of-the art electronic surveillance and multifactor access control systems. Data centers are staffed 24×7 by trained security guards, and access is authorized strictly on a least privileged basis. (For more information, please visit Amazon’s AWS Security center page; http://aws.amazon.com/security/)
Virtually speaking, our environment exists in an Amazon Virtual Private Cloud (VPC), utilizing VPC Security Groups to restrict access to necessary applications and developers, both via SSH-2 RSA encrypted access and restricted IP/PORT access.
4. Is the data encrypted at rest?
No.
5. Is the data stored in a shared format with other customers?
Each client’s game instance has unique data tables, completely separate from other game instances. This unique data is never shared or intermixed at a storage or application level.
6. How is the separation done if the data is stored with other customers’ data?
Our database schema is specifically designed to keep all game instance data separated in unique data tables, this information is never used or available across instances.
7. Is any medium containing the data transferred by third parties? (Like shipping disks, servers, etc.)
No.
8. Is the data backed up? If so, how and how long the backups are kept?
Database snapshots are created nightly, and kept available for 7 days.
Data Use
1. Is our data transferred to third parties other than Knowledge Guru? If so, under which condition and how it is transferred?
No.
2. What kind of authentication is done to access the data? (For admins and for users)
Our Amazon AWS environment uses 1024-bit SSH-2 RSA keys for admin authentication as well as restricted IP/PORT access for approved access locations. User’s access data only through the application interface, via HTTPS/SSL.
Data Destruction
1. After the end of subscription how long does Knowledge Guru hold our data?
We hold customer data after subscription termination for a period of approximately 30 days prior to removal. This period may be extended depending on the potential status of subscription renewal or client need.
2. How is the data removed from the Knowledge Guru’s mediums?
Relevant database tables are dropped and any unique application files, folders, or media are recursively removed from the system.


